What is Security Onion?
Security Onion is a free and open-source Linux distribution designed for intrusion detection, network security monitoring, and log management. It is based on Ubuntu and provides a comprehensive platform for security professionals to monitor and analyze network traffic, detect potential threats, and respond to incidents. With its robust feature set and user-friendly interface, Security Onion has become a popular choice among security teams and IT professionals.
Main Features of Security Onion
Some of the key features of Security Onion include:
- Network traffic analysis and monitoring
- Intrusion detection and prevention
- Log management and analysis
- Security information and event management (SIEM)
- Compliance monitoring and reporting
Installation Guide
Hardware Requirements
Before installing Security Onion, ensure that your system meets the minimum hardware requirements:
| Component | Minimum Requirement |
|---|---|
| CPU | 2 GHz dual-core processor |
| RAM | 4 GB |
| Storage | 20 GB free disk space |
| Network | 1 GbE network interface |
Installation Steps
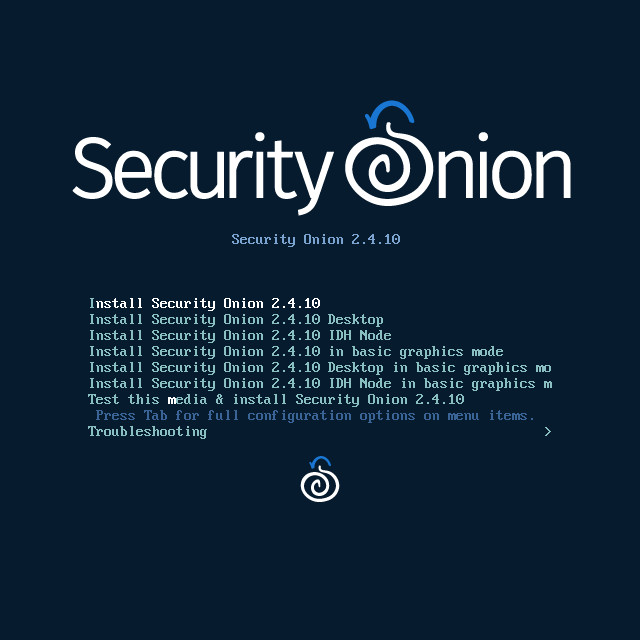
Follow these steps to install Security Onion:
- Download the Security Onion ISO file from the official website.
- Create a bootable USB drive using the ISO file.
- Insert the USB drive into the target system and boot from it.
- Follow the on-screen instructions to complete the installation process.
Security Onion Snapshot and Restore Workflow
What is a Snapshot?
A snapshot is a point-in-time image of the Security Onion system, including all configurations, logs, and data. Snapshots can be used to restore the system to a previous state in case of a failure or corruption.
Creating a Snapshot
To create a snapshot, follow these steps:
- Log in to the Security Onion web interface.
- Navigate to the